Hey there folks,
I’m trying to figure out how to configure my UFW, and I’m just not sure where to start. What can I do to see the intetnet traffic from individual apps so I can know what I might want to block? This is just my personal computer and I’m a total newbie to configuring firewalls so I’m just not sure how to go about it. Most online guides seem to assume one already knows what they want to block but I don’t even know how/where to monitor local traffic to figure out what I can/should consider blocking.
If you really need one take white list approach. Block everything you don’t need and only open what you need. Have fun finding out what you need.
Lots of good answers here but I’ll toss in my own “figure out what you need” experience from my first firewall funtime. (Disclaimer: I used nftables – it should be similar to ufw in terms of defaults though).
- Right off the bat, everything unneeded was blocked. I “needed” no configuration, except for maybe…
- Whatever CUPS runs on (when I use it)
- Sometimes I ran
python -m http.server– I unblocked port 8000 for personal use. - I chose to unblock port 53 (DNS). I wanted to connect to another computer via hostname IIRC (e.g. connecting to raspberry-pi.local. I might be misremembering this though).
- At one point I played with NGINX – that’s port 80 (HTTP) and port 443 (HTTPS).
- SSH was already permitted (port 22 – you need root access to enable traffic through ports below 1024 anyway so this wasn’t an issue for running typical apps)
I didn’t use WireShark back then, really. I think I just ran something like
sudo lsof -nP -iTCP -sTCP:LISTENwhich showed me a bunch of port traffic (mostly just harmless language servers).
You don’t have to dive to deep into all the “egress” and “ingress” and whatnot unless you’re doing something special. Or your software uses a weird port. (LocalSend lol)
You’ve got it backwards. A firewall blocks everything, then you open up the ports you want to use. A standard config would allow everything going out, and block everything coming in (unless you initiated that connection, then it is allowed).
So the question you should be asking, is what services do you think you’re going to be running on your desktop that you plan to allow anyone on the internet to get to?
Not entirely clear but perhaps OP is talking about blocking unwanted outgoing reqjests? E.g. anti-features and such since they mention traffic from their apps.
Possibly? The way I read it, it sounded like OP wasn’t really even sure what a firewall does.
What can I do to see the intetnet traffic from individual apps
what I might want to block?
One strategy is to block everything, and open ports as needed. Beware that most guides focus on inbound traffic, whereas you seem to be focusing on outbound traffic.
Why are we recommending Wireshark? That doesn’t make any sense what so ever. If anything have them run a port scan with nmap.
This is crazy advise
wireshark does not work for individual apps, it cannot make a difference between traffic of process a and b.
I’m not sure how Wireshark is related to firewalls honestly. It is mostly a layer 1 and 2 tool
UFW
This is just my personal computer and I’m a newbie to configure firewalls
Leave it alone.
If you want to experiment, set up a VM and experiment there.
Also, if you want to learn about Linux firewalls, go for iptables instead. UFW is easier, yes, but you won’t get the standard way of configuring a Linux firewall, though to be honest, unless you are directly connecting the computer to the internet, you probably won’t need to bother.
And if you are working in an environment where you are dealing with a segmented network with limited access between segments, they will probably already use a separate firewall that is easier to manage centrally than induvidual firewalls running on individual computers
You shouldn’t be touching it, honestly. There’s a firewall at your router. It should be responsible for blocking incoming traffic. Firewalls on individual machines are for servers where you know exactly what’s going in and out. I don’t have a firewall on my desktop or laptop.
You will spend the best years of your life chasing random network connections if you block everything by default.
This is good sane advise. I think a lot of people here don’t understand networking
You don’t need a firewall on a typical desktop computer. You only need them on routers and servers.
That is because your personal computer is not actually on the internet. It is on a local network (LAN) and it talks only to your router. The router is the computer connected to the internet, and it has a firewall.
The question highlights a classic misunderstanding about networking that IMO should be better addressed. I was like OP once, and panicking about this pointlessly.
Addendum: You’re all replying to OP as if they’re a sysadmin managing a public-facing server. But OP says clearly that they’re just a beginner on a PC - which will almost certainly be firewalled by their router. We should be encouraging and educating people like this, not terrorizing them about all the risks they’re taking.
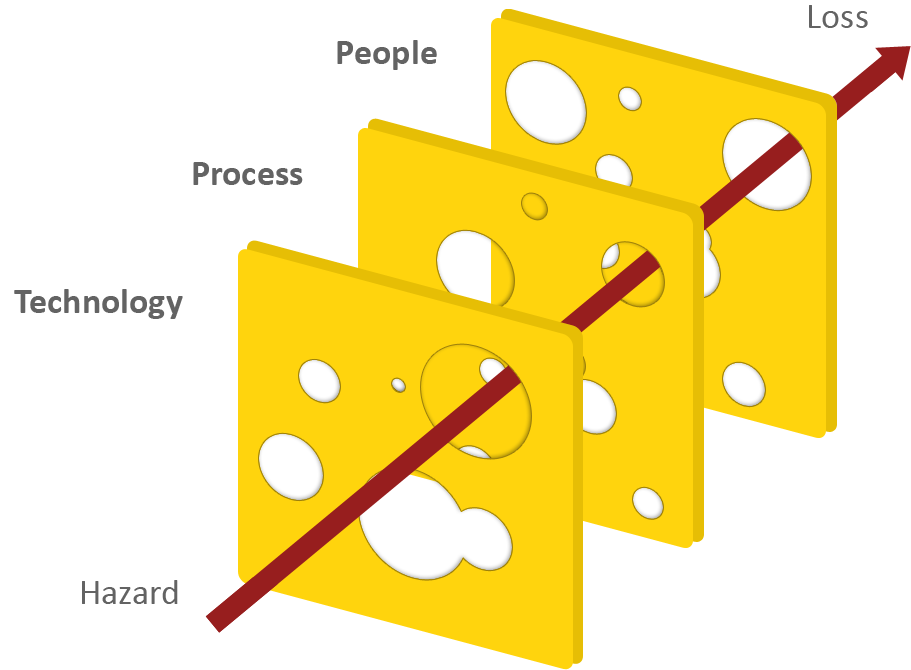
I think you need a bit of Swiss cheese in your security philosophy. Relying only on your router’s firewall is a single point of failure. If it fails you are screwed. Relying on multiple layers means if one layer fails, another one might save you.
Well, screwed I will be, then. I’m not going to waste my life babysitting a bespoke firewall on my Ubuntu Desktop.
And it seems like a bad idea to be telling beginners on Ubuntu or Mint whatever that their “security philosophy is flawed” and they must imperatively run these 10 lines of mysterious code or else bad things will happen.
This whole discussion looks like a misunderstanding. OP is not a sysadmin on public-facing server. They are a beginner on a laptop at home.
I mostly agree with you, but given it’s a laptop that may not always be at home. It is wise to consider enabling the firewall when connecting to other untrusted networks like Starbucks




